Invicti Web Application Security Scanner Review
In this Invicti Web Application Security Scanner review you will find Invicti’s features, pricing details, functionality and many more.
Website hacks have been a significant concern for many years now, and hackers are always looking for ways to hack websites. As a result, securing web applications is an integral part of any security strategy.
That is where web application security scanners come into play.
A web application security scanner, also known as a web application vulnerability scanner, is used to detect threats and protect websites from malicious hackers.
Web Application Vulnerability Scanners are classified as DAST (Dynamic Application Security Testing) tools.
Today in this post, we review Invicti Web Vulnerability Scanner (WVS).
What is Invicti Web Vulnerability Scanner
Invicti is an easy-to-use web application vulnerability scanner helps you to identify security vulnerabilities in your web applications, so that you can fix them as soon as possible.
Invicti’s software scans the target URL and finds out where there are potential security holes which could be exploited by hackers .
Invicti scans web applications to look for security vulnerabilities such as OS Command Injection, Remote File Inclusion/SSRF, Path Traversal, SQL Injection, Reflective XSS, Unvalidated Redirect in web applications, web API.
Invicti can detect vulnerabilities in modern applications. This does not matter what architecture or platform the application is built on. Once Invicti detects any vulnerability it will provide proof of an exploit by verifying whether or not the scan was false positives.
Invicti Editions
Invicti web application security scanner comes with two editions
#1. Invicti Enterprise
It is a multi-user enterprise and scalable solution. It is available either On-Prem or On-Demand solution.
#2. Invicti Standard
It is a single user Windows application.
Note: To provide highly accurate scan results, Invicti uses the same Proof-Based Scanning technology in both the editions.
Invicti Features
- Invicti team provides onboarding assistance and training.
- The user interface is simple and easy to navigate.
- With Invicti’s unique dynamic + interactive (DAST + IAST) scanning approach, you can scan the corners of your apps and get increased visibility.
- Integrates with tools such as JIRA, Bugzilla, and GitHub.
- It provides reporting templates for OWASP Top 10, PCI, HIPAA, and other compliance requirements.
- It support SSO, 2FA, and OTP authentication.
- Automatic scanning of password-protected areas.
- Allows to build personalized security reports with its custom reports API.
- Automatically verifies identified vulnerabilities, proving they are real and not false positives with its Proof-Based Scanning technology.
- It makes running scans easy, with no need for the knowledge of complicated frameworks or programming languages.
- Comes with both On-Prem and On-Demand deployment options.
- It allows unlimited users as well as unlimited scanning models.
Don’t miss: Acunetix Web Application Security Scanner Review
Invicti Integration
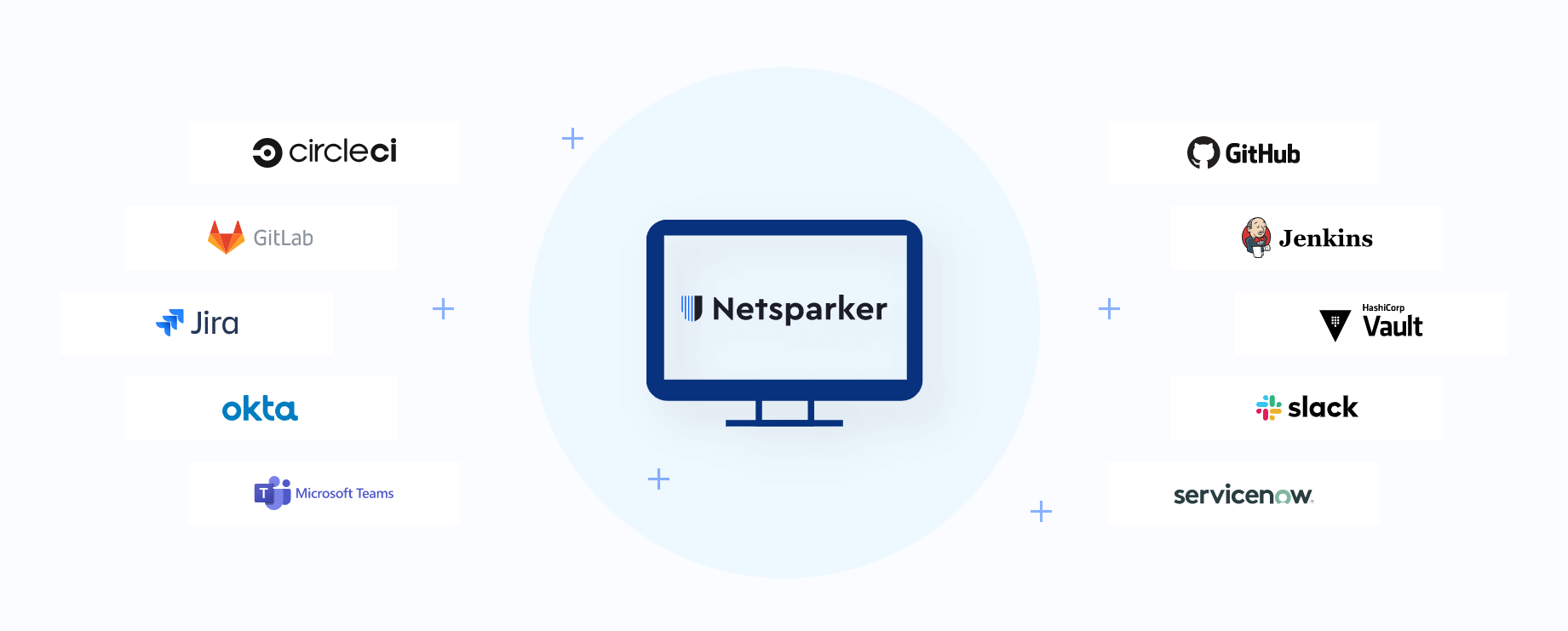
It can be integrated with the following
- Issue Tracking Tools like BugZilla, FogBugz, JIRA, Redmine, YouTrack, Bit Bucket, Azure Boards, Clubhouse, Freshservice, GitHub, GitLab, Kafka, Kenna, PagerDuty, Pivotal Tracker, ServiceNow,Splunk, TFS,Unfuddle.
- Project Managment Tools like Asana, Trello.
- Continuous Integration Systems like Jenkins, GitLab CI/CD, Circle CI, Bamboo, Travis CI, TeamCity, Azure Pipelines, GitHub Actions, UrbanCode.
- Communication Tools like Slack, Microsoft Teams, Mattermost.
- Web Application Firewall (WAF) like AWS, Cloudflare, F5 BIG-IP, FortiWeb, Imperva SecureSphere, ModSecurity.
- Single Sign-On (SSO) Providers like Azure Active Directory, Google, Microsoft ADFS, Okta, PingFederate, PingIdentity, SAML.
- System for Cross-domain Identity Management like Azure Active Directory, Okta.
- Privileged Access Management like CyberArk Vault, HashiCorp Vault
- API like Invicti API, Webhooks, Zapier.
Invicti Pricing
You can contact Invicti team for pricing details.
Invicti Tutorial
#1. How Invicti Works
Invicti scans the app after every change in the code.
Invicti Scanning Engine will run a scan on a website and determine any security vulnerabilities, i.e., XSS, Path Traversal, etc., that need to fix.
If Invicti finds any issue, then it creates that issue in the Issue Tracking System.
Assign the issue to a developer and let them know by sending a notification.
Check that the application is secure by rescanning after the development team fixes the issue.
#2. How to Scan a Website in Invicti Standard
- Open Invicti Standard.
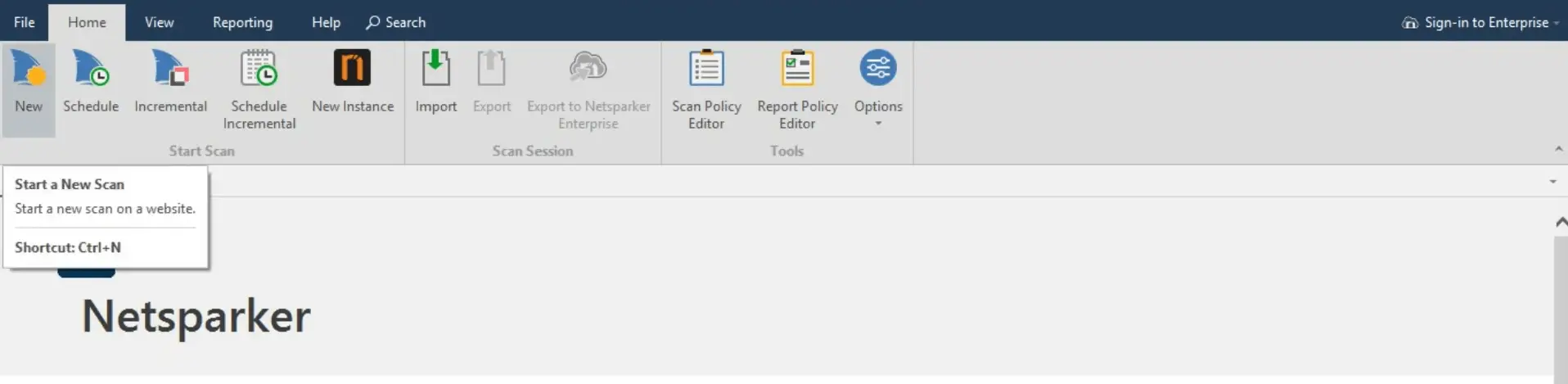
2. Click on ‘Start a New Scan’ in the Home Tab.
3. The ‘Select a New Website or Web Service Scan’ dialog is displayed.
4. In the ‘Target Website or Web Service URL’ field, enter the URL of the website you want to scan.
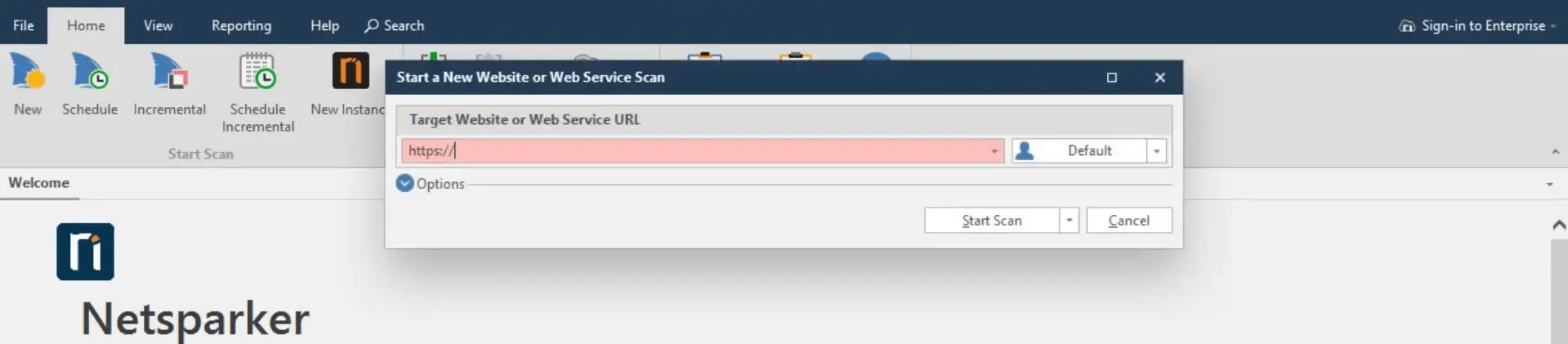
5. Configure the Scan Policy, Invicti Standard Scan Options Fields and Authentication as required.
From the Crawl and Wait drop-down, select Start Scan.
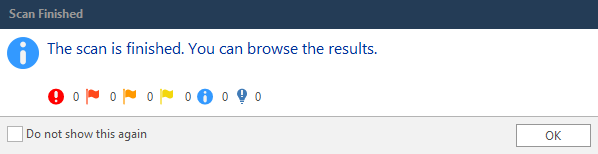
6. When the scan is completed, and the Invicti Standard window is in the background, a Scan Finished information dialog is displayed.
#3. How to Generate Exploits for Vulnerabilites in Invicti Standard
- Open Invicti Standard
2. From the ribbon, select the File tab. Local Scans are displayed. Doubleclick the relevant scan to display its results.
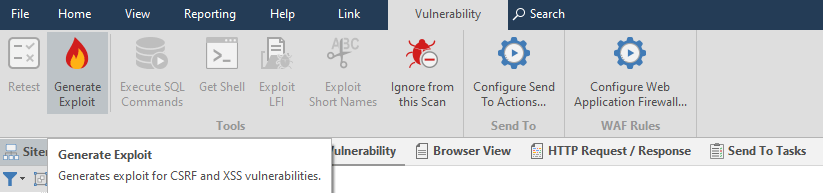
3. From the Sitemap or Issues panel, select an XSS or CSRF vulnerability.
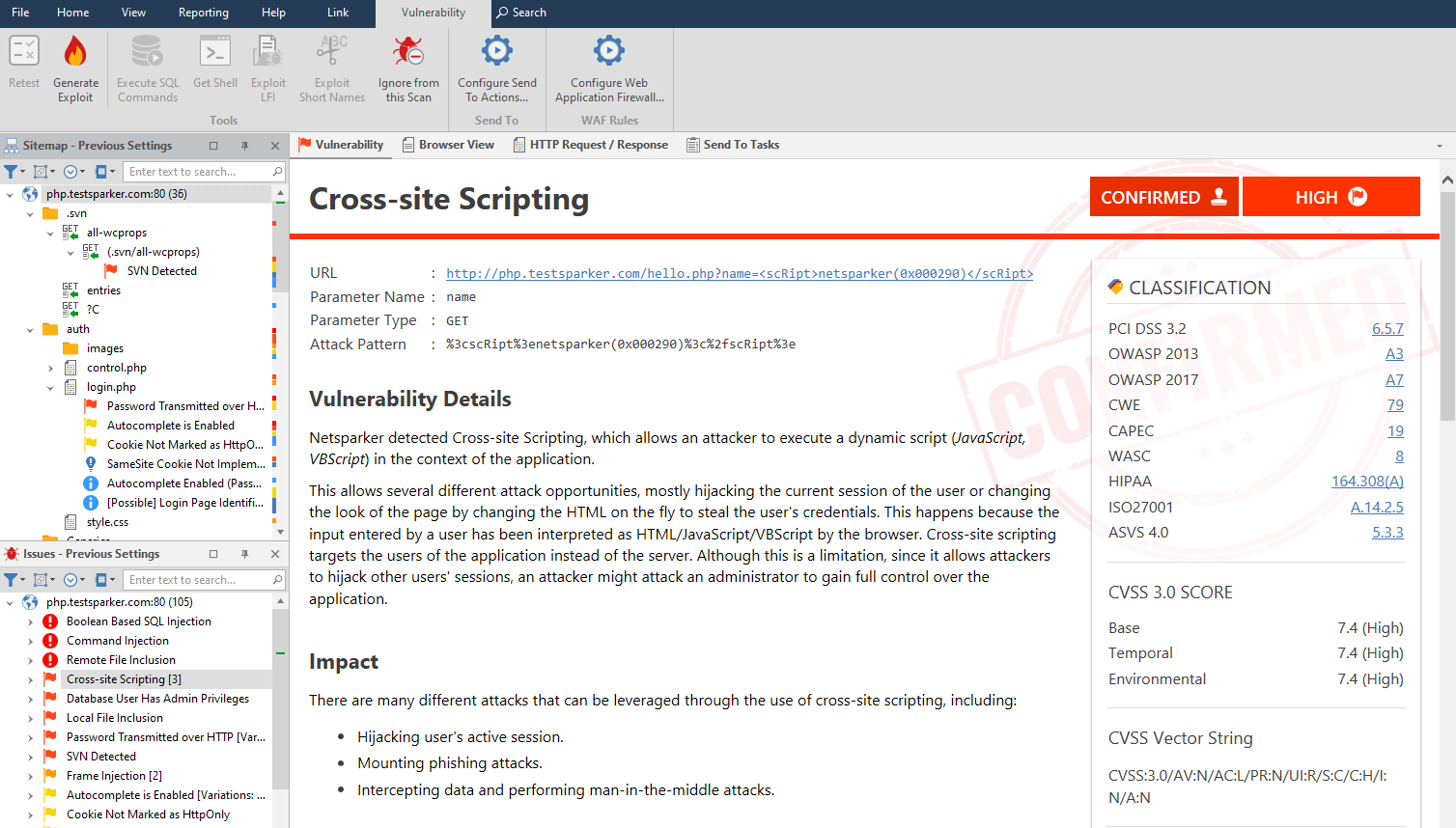
4. In the Vulnerability tab, click Generate Exploit.
5. The Save As dialog box is displayed.
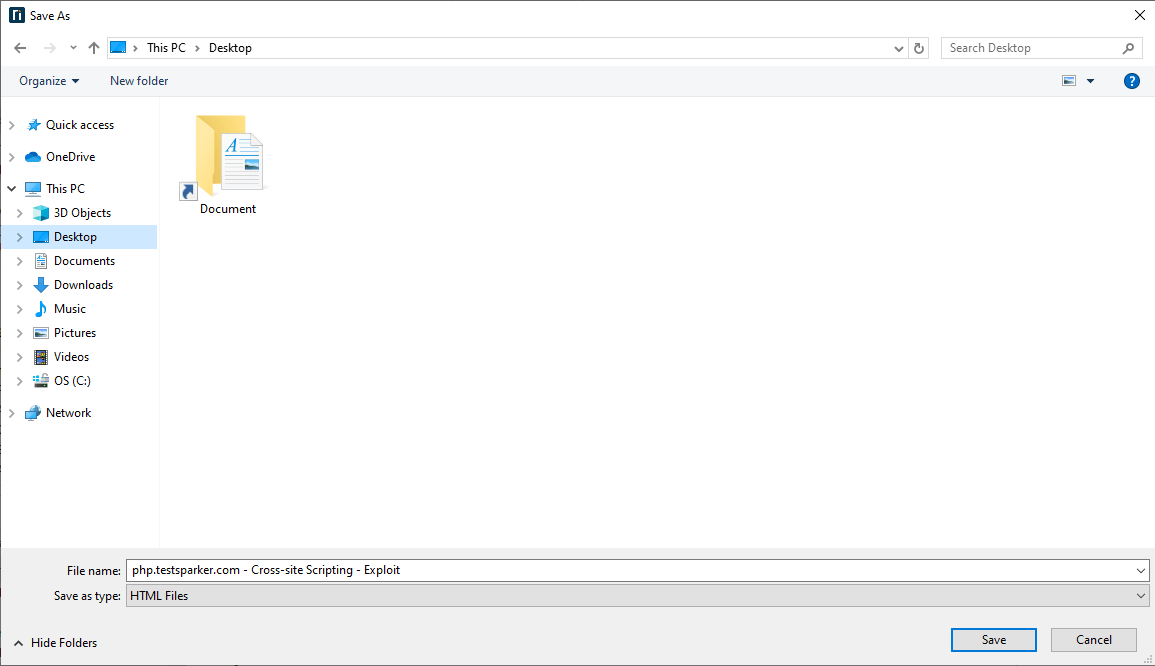
6. Select a save location and click Save.
7. You can view the HTML file in the Save location.
Conclusion
Invicti Web Application Security Scanner is a powerful tool used by the world’s top enterprises to scan for vulnerabilities in web applications. It has helped organizations identify and fix security flaws that would have otherwise gone unnoticed. It has 1000+ active customers and scans tens of thousands web applications each month.
I hope this review will help you in choosing Invicti as your organizations Security testing tool.
Don’t forget to try Invicti Web Vulnerability Scanner. Share your working experience on this tool here in the comment section below with us.
Images source Invicti.
Related posts:
- Acunetix Web Application Security Scanner Review
- Secpod SanerNow Review
- Astra Pentest Review
- Best Dynamic Application Security Testing (DAST) Software
- Best Vulnerability Assessment Scanning Tools
- Best Penetration Testing Companies
- Best Nessus Alternatives
- Best Burp Suite Alternatives
- Best Penetration Testing Tools
- Penetration Testing Guide
- Best Security Testing Tools
- Best Web Application Testing Tools