What is Data Exfiltration? Definition, How To Prevent
Data exfiltration is a growing concern for businesses of all sizes as the value of sensitive data continues to increase.
This can include confidential financial information, intellectual property, customer data, and personal employee information.
In addition to the financial and reputational cost of data breaches, organizations may also face legal consequences for failing to properly secure sensitive data.
What is Data Exfiltration?
Data exfiltration, also known as data extrusion, data exportation, data theft, or data leakage, is the unauthorized transfer or removal of confidential data from personal or corporate devices, such as computers or mobile phones.
Data exfiltration can be done in two ways – manually, where a person with physical access to a computer conducts it, or automatically, where malicious programming is used to conduct it over a network.
What are the different ways of Data Exfiltration?
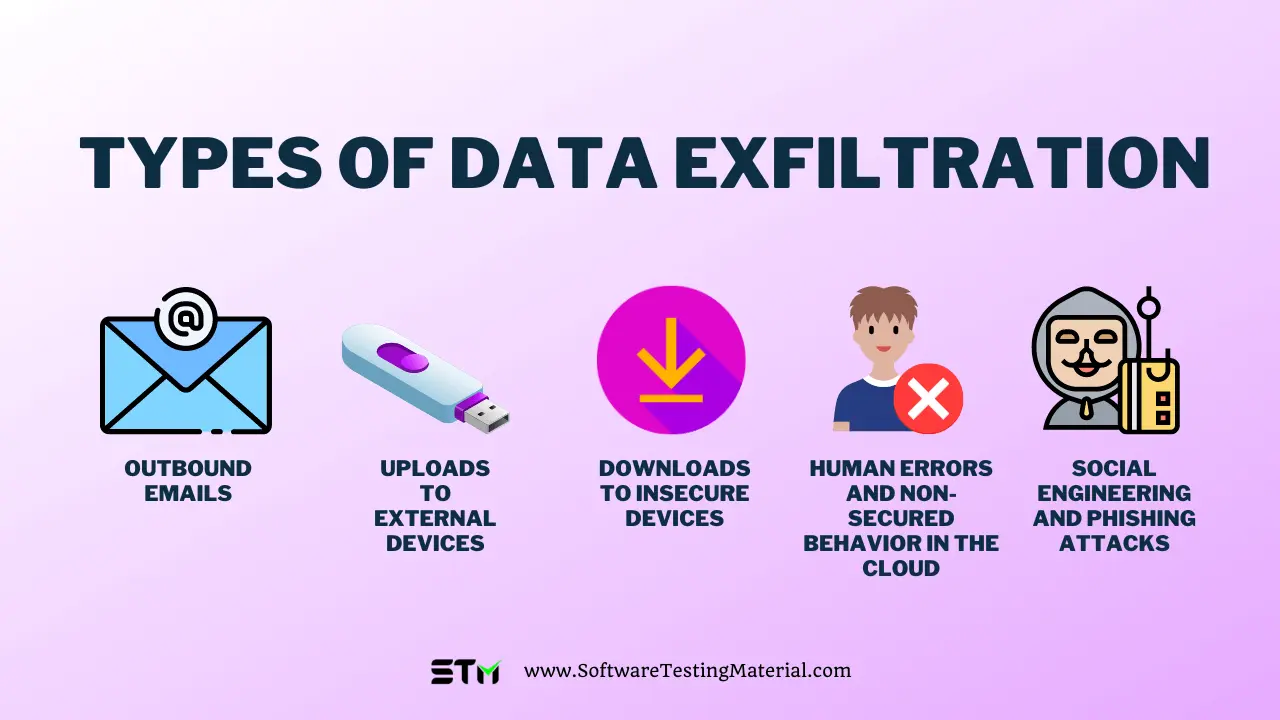
Different ways of data exfiltration are
- Through Outbound Emails – Data leaves the network through emails or messages.
- Through Uploads to External Devices – Malicious insiders can exfiltrate data from a secure device by downloading it and transferring it onto an external device without authorization.
- Through Downloads to Insecure Devices – This might be an accidental insider threat. The malicious actor gains access to sensitive data on a trusted device and transfers it to an insecure device.
- Through Human Errors and Non-Secured Behavior in the Cloud – If an authorized user uses an insecure way to access cloud services, it can allow a malicious actor to modify virtual machines, install harmful code, and send malicious requests to the cloud services.
- Through Social Engineering and Phishing Attacks – These are common methods used by hackers to deceive victims into providing their account credentials and downloading malware.
How to prevent Data Exfiltration?
The main aim of DLP is to stop data exfiltration.
Failing to control information security can lead to data loss that could cause reputational and financial damage to an organization.
DLP software monitors the movement of data inside the network, on employee devices, and on the corporate infrastructure to prevent data exfiltration. In case of any risk of data leaving the corporate network, DLP can send alerts, change data permissions, or even block the data.
Conclusion
Overall, data exfiltration is a serious threat to businesses and their sensitive data. To prevent data exfiltration, businesses can employ a variety of security measures, including DLP solutions. Check out our detailed comparison of the best DLP software list.
Related posts:
- Best Device Control Software
- Best Digital Guardian DLP Alternatives And Competitors
- Best Forcepoint DLP Alternatives
- Best McAfee DLP Alternatives
- Best Symantec DLP Alternatives