Top 10 Web Application Security Vulnerabilities
The Open Web Application Security Project (OWASP) is a nonprofit foundation that has come to define basic cyber security standards – for private organizations, government, and for pentesters. The organization itself consists of tens of thousands of members, many of whom are volunteers, who deliver community-led and open-source software and security projects on a global level. Today, OWASP functions as one of the most-used and most-reliable sources of security information, technology, and guidelines.

What is OWASP?
OWASP stands for the Open Web Application Security Project. OWASP is an online open community dedicated to improve the security of software. In the area of web application security, it creates articles, methodologies, documentation, tools, and technologies.
Don’t miss: Best Security Testing Tools
What is the OWASP Top 10?
The OWASP Top 10 comprises the “top 10 application security vulnerabilities”, released on a rolling basis, as the most likely vulnerabilities appear. This list is used as a guideline for pentesting, for cybersecurity, and for internal risk assessment, based on the likelihood of risk associated with a particular vulnerability. The report is based on consensus from security experts, based on the frequency of discovering those vulnerabilities and the magnitude of potential impact in case those vulnerabilities are breached.
The latest iteration of the OWASP Top 10 is 2021, which was introduced in the last week of October 2021. The list introduces 3 new vulnerability categories and removes old ones, and ranks risks based on likelihood of occurrence. Its intent is to offer security professionals, developers, and pentesters insight into prevalent risks, with recommendations for remediation offered by security professionals.
How Does the OWASP Top 10 Work and Why Is It Important?
Most developers and security experts rely on the OWASP Top 10 as a key checklist to ensure their app or code meets basic security standards. Passing OWASP Top 10 assessments usually means ruling out the most likely vulnerabilities, which can provide a significant increase in security for any web application. In addition, pentesters and auditors often use compliance with the OWASP Top 10 as a measure of whether the organization has basic security measures in place at all. For example, many auditors use the Top 10 as a basic requirement for meeting compliance standards. In many cases, this requirement is worked into regulatory compliance as well – with some compliance standards referencing the OWASP Top 10.
In addition, the OWASP Top 10 is assessed and updated periodically, as top risks change. That makes the list a living document, which changes as risks, vulnerabilities, and common exploits change.
Don’t miss: Best Vulnerability Assessment Tools
The Top 10 Web Application Security Vulnerabilities
The 2021 OWASP Top 10 Web Application Security Vulnerabilities includes:
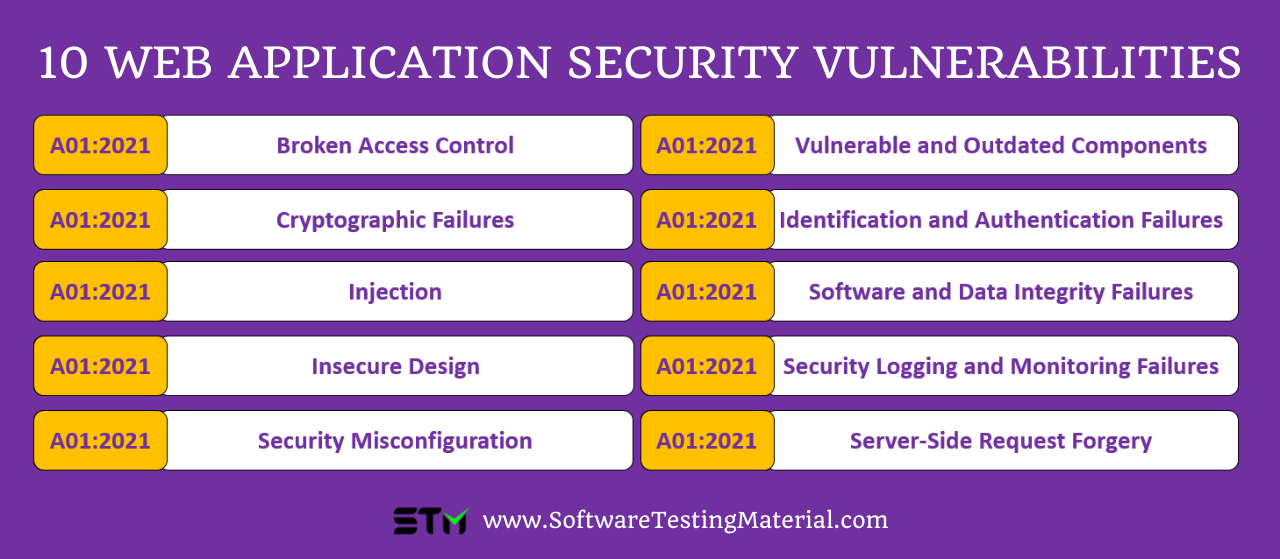
- A01:2021-Broken Access Control
- A02:2021-Cryptographic Failures
- A03:2021-Injection
- A04:2021-Insecure Design
- A05:2021-Security Misconfiguration
- A06:2021-Vulnerable and Outdated Components
- A07:2021-Identification and Authentication Failures
- A08:2021-Software and Data Integrity Failures
- A09:2021-Security Logging and Monitoring Failures
- A10:2021-Server-Side Request Forgery
A01:2021-Broken Access Control
Broken access controls jumped to the top of the OWASP Top 10 list for 2021, up from #5 in 2017. Broken access controls normally consist of failures to control user permissions. Therefore, failures can result in unauthorized information disclosure, modification or destruction of data, or user accounts having access to permissions and data they should not have. That becomes especially problematic when abusable from external accounts or when a hacker gets ahold of a user account. OWASP shows 34 Common Weakness Enumerations (CWEs) mapped to broken access controls, with over 318,000 occurrences of broken access control found.
For example:
- Bypassing access control checks by modifying the URL, internal application, HTML page, or API
- Allow the user to change their own records or another user’s records
- Elevation or privilege
- Metadata manipulation (e.g., JWT access control manipulation)
- CORS misconfiguration
Prevention: Regularly pentest applications. Integrate secure-by-design principles. Use basic security functions like denying user access to functionality by default, using control lists with role-based authentication mechanisms, and blocking rather than just hiding functions.
A02:2021-Cryptographic Failures
In 2021, OWASP updated Sensitive Data Exposure to cryptographic failures, switching focus to the cause rather than the problem. This category includes incidents in which sensitive data is leaked or accidentally exposed, normally through issues like:
For example:
- Sensitive data is transmitted or stored n clear text (databases, files, etc.) and not hashed
- Use of old or weak algorithms
- Poor or default encryption keys, re-use of encryption keys (especially when keys are lost)
- Server certificates not being validated
- Encryption not being enforced
Prevention: Roll out standard and tested cryptography solutions and enforce them across the application. Ensure that all data used or dealt with by the application is encrypted at rest and in transit. Make sure you hash and salt sensitive data such as passwords. And, ensure you’re not caching sensitive data.
A03:2021-Injection
While injection has been #1 in the OWASP Top 10 list for years, it’s now #3. OWASP claims 94% of applications show some form of injection vulnerability. Unlike 2017, this category now also includes cross-site scripting. This includes risks created when:
For example:
- User-supplied data is not validated or sanitized by the application
- The interpreter directly uses either dynamic queries or non-parameterized calls without context-aware escaping
- Objectionable-relational mapping allows hostile data to extract sensitive data
- Structure can be found in the SQL or command, allowing malicious dynamic queries, commands, or stored procedures.
Prevention: Pentest to assess SQL and ORM as well as API security. You also want to use a safe API, which avoids using the interpreter. Integrating positive server-side input validation, specific escape syntax for residual dynamic queries (tables, column names, etc. Cannot be escaped), and using LIMIT and other SQL controls within queries to prevent mass-disclosure of records are some mitigation measures.
A04:2021-Insecure Design
Insecure Design is another category new to the Top 10 for 2021. This category refers to all risks created by insecure design or architecture. The idea is to promote secure-by-design, threat modeling and reference architectures, which reduce vulnerabilities “by design”. This category is extremely broad by nature, with significant steps required to mitigate the CWEs.
For example:
- Collecting protection requirements for confidentiality, integrity, availability, and authenticity of all data assets expected for the business logic
- Secure design
- Secure development lifecycles
- Establish and use secure design patterns from a library or paved road components list
- Use thread modeling
- Integrate security language and controls into user stories
- Test and validate all critical flows
- Segregate tenants
- Segregate tier layers
- Limit resource consumption per user/per service
A05:2021-Security Misconfiguration
Security misconfigurations are the fifth most common web application vulnerability, with an incident rate of 4%. The category includes risks related to configuration of servers, features, handling, etc.
For example:
- Improperly configured permissions
- Missing security hardening
- Default accounts / passwords are still in place
- Overly informative error messages
- Error handling reveals stack traces
- Security features are disabled or not configured
- Security settings are not set to secure values
- No security headers/directives/not set to secure values
- Software is out of date
Prevention: Preventing these types of issues normally relies on scanning, periodic hardening processes, and a good security policy. For example, assessing security and configurations on a quarterly basis ensures the application stays secure across updates. Many applications, such as Azure and Google Cloud, offer integrated security scanners that check for common misconfiguration issues.
A06:2021-Vulnerable and Outdated Components
Vulnerable and Outdated components are so common that the OWASP Community Survey listed it as the second most found vulnerability. The official OWASP Top 10 2021 puts it at #6. These vulnerabilities commonly occur in platforms where there is no accountability for who is in control of updating and maintaining component versions. For example:
For example:
- Software is unsupported or out of date
- No one knows what version components are (client and server side)
- There are no scanners in place to check for out-of-date components
- Fixes and upgrades to platforms, frameworks, and dependencies are not updated in a timely manner. E.g., you have a monthly or quarterly update cycle rather than integrating updates as they appear
- Developers do not test the compatibility of updated, upgraded, patched libraries
- Component configurations are not secured
Prevention: Preventing these types of issues normally starts with integrating a scanner, a process to continuously inventory and update components, and a secure policy with best practices. This should include checking components and their dependencies, using software composition analysis tools, ensuring components are only obtained from official sources, and monitoring for unmaintained components.
A07:2021-Identification and Authentication Failures
Identification and Authentication Failures (previously Broken Authentication) relates to all instances in which users can abuse credentials or sessions to gain access to sensitive data or gain access beyond allowed access for that user. These include:
For example:
- Credential stuffing attacks from a list of valid usernames/passwords
- Brute force/automated attacks
- The application allows default or common passwords
- Passwords are stored in plain text or weakly hashed
- There is no multi-factor authentication
- Session identifiers in URLs
- Session identifiers are re-used
- Session IDs are not invalidated during logout or during inactivity
Prevention: Preventing authentication vulnerabilities normally relies on enforcing good password policies for users, internal users, and employees. That means cross-checking passwords against weak passwords, ensuring passwords align with NIST guidelines, and enforcing multi-authentication for sensitive data. Hardening recovery pathways, limiting login attempts, and using a server-side built-in session manager are also important steps.
A08:2021-Software and Data Integrity Failures
Software and data integrity failures are the third and final new category in the 2021 OWASP Top 10. This new category covers integrity failures related to code and infrastructure, such as auto-updating applications without verifying the integrity of the update or its impact on security configurations.
Prevention: In most cases, preventing this type of problem involves integrating security standards into the software delivery pipeline. For example, using digital signatures to verify that updates are from the expected source, ensuring libraries and depositories are from trusted sources, ensuring a software supply chain security tool is in place, and using a review process for code and configuration changes. In most cases, it’s also ideal to integrate CI/CD pipeline segregation and to ensure that no unsighted or unencrypted data is sent to untrusted clients without an integrity check.
A09:2021-Security Logging and Monitoring Failures
Logging and monitoring failures are difficult to test for and difficult to catch, but still represent major security vulnerabilities for most web applications. In most cases, vulnerabilities occur when logs are improperly stored, not logged, or only stored locally. You’ll also run into issues when there are no alerting thresholds or automated response escalation policies in place.
Prevention: Preventing security and logging monitoring failures means implementing logs, ensuring that all necessary data is logged, and setting automated alerts to escalate issues for a human review if they set off red flags. For example:
- Ensure all logins, failed logins, transactions, warnings, and errors, etc., generate log messages
- Use DAST to scan logs for issues
- Set up alerts to detect, escalate, and send alerts for suspicious log activity
- Encode log activity to prevent injection
- Use stronger audit trails with integrity controls for high-value transactions
- Integrate an incident response and recovery plan, such as NIST 800-61r2 etc.
A10:2021-Server-Side Request Forgery
Server-side request forgery came in #1 in the Top 10 Community Survey, moving it to #10 in the official list. This relatively new vulnerability occurs when web applications fetch resources without validating the user-supplied URL – allowing attackers to manipulate the application.
Prevention: Mitigating Server-side request forgery normally means taking steps to reduce damage, ensuring client-supplied data is sanitized, and disabling redirects. For example, establishing ownership and lifecycle for firewall rules based on applications, log all accepted and blocked network flows on firewalls, segment resource access functionality on separate networks to reduce the impact of a breach, checking URL consistency, blocking sending raw responses, etc.
Final thoughts
OWASP Top 10 is a valuable resource for developers, security experts, and pentesters. It serves as a basic guideline for security – as it represents the most common, most likely, and most impactful vulnerabilities. Hardening a web application against these vulnerabilities can considerably increase security and therefore decrease the likelihood and/or severity of a breach. And, that’s important whether for general application security, for compliance, or for meeting the security needs and expectations of clients and users.
The updates to OWASP Top 10 for 2021 reflect cybersecurity today. OWASP has made changes to update the order of risks, types of risk, and risk naming schemes so they are more representative of cybersecurity as it is today. That means the current iteration delivers a better understanding of vulnerabilities, the nature of those vulnerabilities, and likely associated risks.
However, while OWASP Top 10 is a good place to start, it’s not the end of security. Implementing scanners, engaging in regular pentesting, checking and managing security configurations, and using secure-by-design practices and policies are important for maintaining the security of your application.
Mike Terhaar is the lead pentester and co-founder at Cyver.io. With 20+ years of experience in cybersecurity, he’s worked with banks, government agencies, and high-risk organizations. Today, Mike is working with Cyver to deliver Pentest-as-a-Service and digital pentest delivery.
Related Posts:
- Database Testing Tutorial – Complete Beginners Guide
- Difference between defect, bug, error and failure
- How To Handle Authentication Popup Window Using Selenium WebDriver
- Best Data Loss Prevention Software (Free and Paid)
- Reliability Testing in Software Testing | Complete Guide