What is a Proxy Server | Everything You Should Know
With the increasing concern over online privacy and security, the demand for proxy servers is on the rise. As technology advances, so do the capabilities of proxy servers, making them an essential tool for navigating the vast and complex world of the internet. So the next time you access a website, send a confidential email, or conduct any other online activity, remember that there may be a proxy server working behind the scenes to keep you safe and secure. So it is important to understand how they work and utilize them effectively to protect yourself and your online activities.
Proxies play an important role in ensuring online security and protecting user privacy. They can be used by individuals to bypass content restrictions or by businesses to gather data without revealing their true identity. However, individuals and businesses alike need to use proxies responsibly and ethically, as they can also be used for malicious purposes if not properly managed.
Proxy Server Definition
A proxy server functions as an intermediary between a client and another server, serving as a gateway. It enables clients to access resources from other servers indirectly while safeguarding their privacy and security. The term “proxy” refers to the fact that it represents one entity acting on behalf of another.
Why are Proxy Servers Used?
Proxy servers serve several important functions, but the main reasons they’re used are:
- Primarily, proxy servers are used for security and privacy purposes. Filtering incoming traffic to enhance the security of the company’s network
- Proxy servers can block malicious websites and prevent unauthorized access to sensitive information. Maintaining the privacy of the company’s network
- Additionally, proxy servers can help improve network performance by caching frequently accessed content and reducing bandwidth usage. Speeding up resource access by utilizing a cache.
How Does a Proxy Server Work?
Proxies play a crucial role in processing web requests and responses by routing and securing internet traffic.
- When a client sends a request to access a resource, it first goes to the proxy server.
- The proxy server then evaluates the request and either forwards it to the intended web server or blocks it if it deems the request as potentially harmful.
- The response from the web server is then sent back to the proxy server. The proxy server extracts the data and performs a thorough malware check to ensure its integrity.
- After being marked as safe, the data is then forwarded to the client.
Advantages of Using a Proxy Server
- Enhanced Security: Proxy servers act as a barrier between clients and web servers, providing an additional layer of security by filtering out potentially malicious traffic.
- Anonymity: By hiding the client’s IP address, proxy servers can help protect their identity and keep their internet activity private.
- Improved Performance: Caching frequently accessed content on a proxy server can significantly reduce bandwidth usage and improve network performance.
- Access Control: Proxy servers can be configured to restrict access to specific websites or content, allowing organizations to control internet usage and ensure compliance with company policies.
Types of Proxy Servers
There are several types of proxy servers, each with its own specific features and use cases:
- Forward Proxy: This type of proxy server is used by clients to access resources from the internet. It acts as an intermediary between the client and the web server, allowing for increased security and anonymity.
- Reverse Proxy: This type of proxy server is used by web servers to access resources from clients. It can be used for load balancing and caching, improving overall server performance.
- Open Proxy: This type of proxy server is accessible to any user on the internet. It is often used for bypassing internet restrictions and hiding one’s identity.
- Transparent Proxy: A transparent proxy, also known as an inline proxy, is a type of proxy server that does not modify the requests or responses from the client. It is often used for caching and filtering purposes, as it allows traffic to pass through without any modifications and appears as though it is coming directly from the user. This type of proxy offers little privacy as it does not conceal any information about the user’s identity.
- Anonymous Proxy: This type of proxy server is used for increasing anonymity and privacy. It removes identifying information from the client’s request, making it difficult to trace back to the original user.
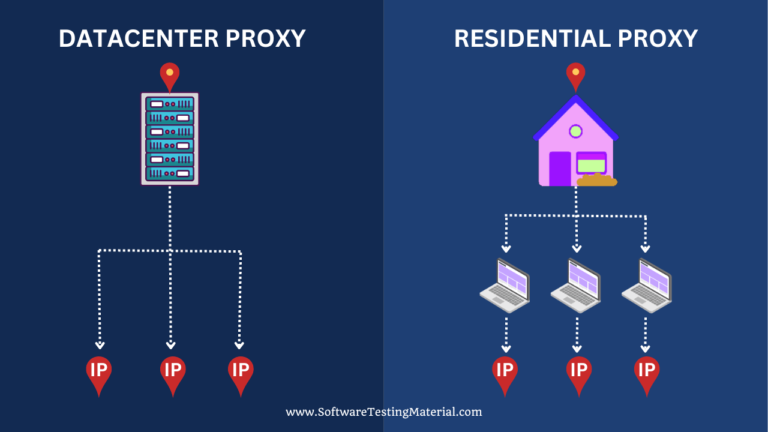
- Data Center Proxy: This type of proxy server is used by businesses to gather data from web sources without revealing their real IP address. It is deployed within a data center and can be used for market research, price monitoring, and other data-driven activities.
- Residential Proxy: This type of proxy server uses IP addresses assigned to real residential networks, making them indistinguishable from regular users. It is often used for tasks that require high-level anonymity and non-detection, such as web scraping and social media marketing.
- High Anonymity Proxy: This type of proxy server offers the highest level of anonymity as it hides all identifying information from the client’s request. It is often used for sensitive activities such as accessing restricted content or conducting confidential transactions.
- Distorting Proxy: This type of proxy works as an intermediary, pretending to be you by using a fake IP address and identifying itself as a proxy. It’s like an anonymous proxy but with the added advantage of simulating a different location. This lets you bypass content restrictions and access what you want.
- SSL Proxy: A Secure Sockets Layer (SSL) proxy is a type of proxy server that encrypts all communication between the client and the web server using SSL technology. This allows for secure access to websites and protects sensitive information from being intercepted by third parties.
- Rotating Proxy: A rotating proxy automatically changes the IP address it uses for every request made through it. This provides added anonymity and makes it difficult to trace back the original user, making it ideal for tasks that require a high level of privacy.
- Public Proxy: A public proxy is an open proxy server that can be accessed by anyone. While this may offer some benefits, it also poses a security risk as the server can be easily exploited by hackers.
- Private Proxy: A private proxy is a proxy server that requires authentication to access, making it more secure than public proxies. It also offers better speed and reliability since it is not accessible to the general public.
- Shared Proxy: A shared proxy is a type of private proxy that is shared among multiple users. This can help reduce costs for individuals or businesses who do not require dedicated resources, but it also means that the server’s performance may be affected by other users.
FAQ’s
Are Proxy Servers Similar to VPNs?
Proxy servers and VPNs serve similar purposes but have distinct differences in functionality and security. Proxy servers act as intermediaries, hiding IP addresses and providing some level of anonymity, but they do not encrypt internet traffic. On the other hand, VPNs create secure and encrypted connections, protecting data from interception. VPNs also allow access to geo-restricted content. While both options hide IP addresses, VPNs offer greater security and privacy.
Can my IP be tracked if I use a proxy?
Yes. Using a proxy doesn’t guarantee complete anonymity as your IP address can still be traced. Proxy servers may hide your original IP address, but if their logs are accessed, your activities could be linked back to you. Some proxies also don’t fully conceal your IP address, leaving you vulnerable to advanced tracking techniques. While proxies increase privacy, they don’t offer absolute protection against all tracking methods.
Can my IP be tracked if I use a VPN?
Many people use virtual private networks (VPNs) to protect their online privacy and security. When using a VPN, your internet traffic is encrypted and routed through a remote server, which masks your IP address from the websites you visit.
So can your IP be tracked if you use a VPN? The short answer is no, as long as you choose a reputable VPN service that has strong encryption and a strict no-logging policy. However, there are some situations where your IP may still be traceable.
Conclusion
Proxy servers play a crucial role in enhancing security, improving performance, and providing anonymity for clients accessing web resources. With various types of proxy servers available, it is essential to understand their differences and choose the right type depending on your specific needs. Whether for personal or business use, a proxy server can greatly benefit users by providing a more secure and efficient internet experience. So next time you’re browsing the web, remember that there’s likely a proxy server working in the background to help keep your connection safe and reliable. Keep exploring different ways to optimize your online activities with the help of proxy servers! Happy surfing!
Related posts:
- Best HTTP And HTTPS Proxies List
- Best Residential Proxy Server Service
- Best Online Proxy Websites List
- Best Proxy Server List
- Best VPN Services